We live in a world where offsite data tie-up is more of a need than a deliberation. In such an environment where businesses' data and systems are keen to survival and success, it's vigorous that any third-party assigned to looking after that data does so in a way that signifies best practices where risk assessment and management are concerned. There is more to information security than anti-virus software, firewall technology, and the locking-down of laptops or web servers; the overall approach to information security should be planned as well as operational. While several providers will privilege to adhere to best practices, only those seriously committed will possess an official ISO 27001 certification from G-Certi.
ISO 27001….what it is?
Certification is carried out by an autonomous, accredited certification body. Businesses that are looking for independent certification of their ISMS (Information Security Management System) should always go to an accredited certification body, such as the International Organization for Standardization. The International Organization for Standardization (ISO) has developed a different series of security standards, the rest of which is ISO 27001. ISO 27001 is the replacement for British Standard 7799. Additional International Organization for Standardization in the 27000 family includes IS) 27003, covering security guidance; ISO 2700, for measurements: and ISO 27005, covering risk. On the other hand, claims of obtaining ISO 27001 certification are often misunderstood, or used as a guarantee where they should not be. Certification anticipates that its application will be in the hands of qualified people. Many certification bodies offer ISO 27001 lead auditor training classes.
Description?
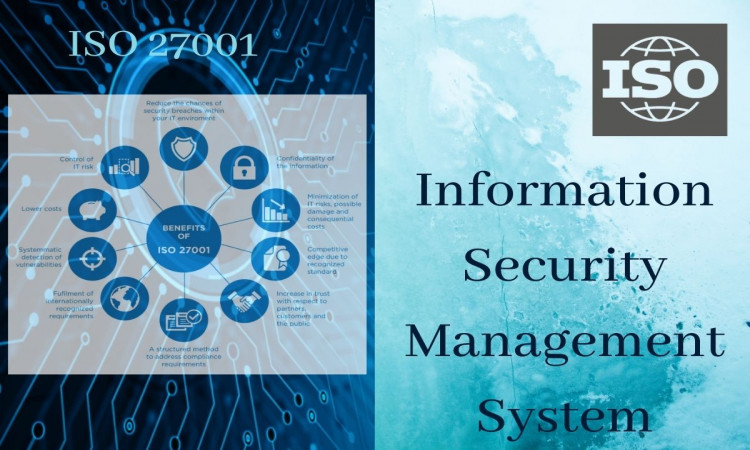
ISO 27001 describes how to construct what ISO calls ISMS. If an ISMS is developed on a standard of acceptance or refusal of the assessed risk, and using 3rd party certification to provide outside confirmation of the level of assurance, is an outstanding tool and will create a management system for information security. ISO 27001 is an Information Security Management System (ISMS) standard, deliberate to make sure the selection of satisfactory and proportionate security controls that protect information assets. Being a formal specification means that it mandates specific necessities, and organizations that have adopted ISO 27001 can therefore be properly audited and certified in compliance with the standard.
ISO 27001 needs that a business does the following;
-Methodically examines information security risks, taking account of any possible threats, liabilities, and associated effects.
-Designs, implements a coherent and comprehensive suite of information security controls and/or additional approaches of risk treatment (such as risk avoidance or risk transfer) to address any potential risks that are believed undesirable.
-Accepts a management procedure to make sure that the information security controls endure meeting the organization's information security requirements continuingly.
Why would a provider become certified?
Like other ISO certifications, ISO 27001 usually comprises an initial two-stage audit process followed by regular assessments. There are also several associated costs, but associations eager to invest time and money into attaining the standard will see it as an investment for the future. While the certification may appear costly to some providers. Organizations that take up the certification commonly find that the staff partaking in the ISO training program gain a heightened level of security information, making them much more conscious of potential security threats. Generally, ISO 27001 certification is a stamp of approval that sets certified organizations apart from their competition.
How do customers advantage?
Wherever offsite data storage is apprehensive, there are many potential safety risks, for example: physical, such as door access and CCTV; logical, which refers to problems like user privileges and data access; and procedural, including areas such as visitor access protocol. By working with an ISO 27001 certified provider, a business can be secure in the knowledge that its data is safe from these risks.
Additional benefits of working with an ISO 27001 certified provider include:
Distinct risk ownership
Avoidance of damage to brand equity
Reliable security policy across the organization
Non-stop security improvement measures
Least risk of data loss through human error.
Data is at the heart of every business and organization, so when a managed service provider from G-Certi manages your data, be sure to work with an ISO 27001 certificated partner. Visit our website for more details.
Leave a reply
Your email address will not be published. required fields are marked *






{{comments.length}} Comments
{{ comment.name }}
{{comment.datetime}} Reply{{comment.message}}
{{ comment.name }}
{{comment.datetime}}{{comment.message}}